NETWORK FORENSICS & INCIDENT RESPONSE
Peace and Security Studies
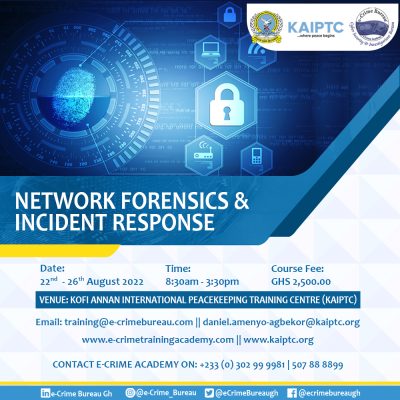
Course Fee: Each participant shall be required to pay a non-refundable fee of ¢2,500 GHS (two thousand, five hundred Ghana cedis). Participants who are coming from outside Ghana would have to make their own travel and accommodation arrangements. Those who will require a visa on arrival will also be responsible for the cost of their visas.
Terms and Conditions:
· The course will be conducted ONLY in English; · Every participant should be fully vaccinated. Those coming from outside Ghana should have proof of adequate health insurance coverage, which should include Covid 19 before travelling to the Centre. Additionally, participants must possess a COVID-19 negative PCR test from an accredited laboratory in the country of origin. The test should have been done not more than 72 hours before the scheduled departure time from the country of origin. KAIPTC will not bear any health or accident costs for any participant.
| In short | |
| Course Date/Duration | 22 August – 26 August 2022 |
| Course Capacity | 25 participants |
| Target Group | The target groups include the following:
African Union, ECOWAS, UN Missions in Africa and other Regional Economic Communities (RECs). a. IT Managers b. SOCs Analyst c. Forensics Investigators /Auditors d. Risk Managers/Analyst e. Security Managers f. Network Administrators g. Criminal Prosecutors h. Police Investigators i. Other individuals interested in gathering digital evidence through forensic investigations. |
| Course Language | English |
| Application Deadline | 18 August 2022 |
| Category
|
Cyber Forensics |
Introduction/Background
The integration of technology-driven solutions in business operations has increased the risk exposure of IT systems of businesses and individuals to network breaches. In most criminal cases, a lot of evidence is dependent on the digital evidence gotten from network forensics, thus investigative businesses must provide evidence that can be admissible in court. The need for professionals to handle incidents of cyber-breaches and network investigations in a timely manner using the right investigation and forensic procedures has become imperative in view of the changing and complex cybercrime landscape. Investigations and analysis conducted by e-Crime Bureau have identified the challenges IT professionals face in responding to and managing incidents within IT environments, especially with complex enterprise systems, integration of third-party applications, cloud computing, and mobile devices, leading to an increase in the exposure of IT environments to digital crimes. This lab-based training will provide practical case study scenarios, best practices, tools, and standard network forensic techniques used to gather digital evidence to build forensic-ready IT environments.
Course Objectives
The main objectives of the course are to:
- To equip participants to gain working knowledge to identify and collect additional evidence based on the existing systems and platforms within a network architecture.
- To enhance participants’ ability to use data from typical network protocols to increase the fidelity of the investigation’s findings.
- To equip participants with skills to analyse network packets and easily identify compromised systems on the network.
- To build the capacity of participants to be able to analyse and examine wireless network traffic using common network protocols to find evidence of malicious activities.
- To equip participants with the necessary skills to prevent incidents from further escalating using information gathered.
Target Group
IT Managers, SOCs Analyst, Network Administrators, Forensics Investigators /Auditors, Risk Managers/Analyst, Security Managers, Criminal Prosecutors, Police Investigators, and other individuals interested in gathering digital evidence through forensic investigations.
Modules of the course
- Introduction to Network Security & Forensics
- Common Network Breaches & Countermeasures
- Network Security Devices and Forensics Evidence
- Evidence Acquisition Techniques and Tools
- Network Packet Capture and Analysis
- Statistical Flow Analysis
- Memory Forensics
- Wireless Security Auditing
- Log Acquisition and Analysis
- Malware Analysis
- Network Threat Intelligence
- Cyber Security Incident Management
How to Apply
Interested applicants are kindly invited to click on the “How to Apply” button in order to fill and submit the online application form and forward it to training@e-crimebureau.com.
Contact
Mary Anna Abakah
Lead, Training
e-Crime Bureau
Tel. 00 233 (0) 0302 999 981
Mobile. 00 233 (0) 50 1304 836 / 50 788 8899
Email: training@e-crimebureau.com
Mrs Marylyn Agblor
Training Coordination Officer
Tel. 00 233 (0) 302 718200 Ext. 1012
Fax. 00 233 (0) 302 718201
Email: marylyn.agblor@kaiptc.org
Email: training.coordination@kaiptc.org
Col Daniel Amenyo-Agbekor
Course Director
Tel. 00 233 (0) 302 718200 Ext. 1035
Fax. 00 233 (0) 302 718201
Email: daniel.amenyo-agbekor@kaiptc.org

